BYOD: What Is A "Bring Your Own Device" Policy?

In today's digital age, data is businesses' and individuals' lifeblood. Thus, ensuring the security of sensitive information is of paramount importance.
While online cloud storage services have increased in popularity, there are times when you have no choice but to bring your own device.
What is BYOD (Bring Your Own Device)?
BYOD (Bring Your Own Device) is a company policy, where individuals are allowed to use their own devices and different types of PC storage at work to transfer data securely.
If proper security measures are not in place this poses the risk of data breaches. In fact, in May 2023 alone, more than 98 million breached records were reported. To mitigate this risk, we've compiled a list of the 12 best secure devices for transporting data physically.
When employees use personal devices, decisions about RAM vs storage matter because limited storage capacity can encourage unsafe practices like using unsecured external drives or personal cloud accounts to move data.
Whether you are a business professional, a student, or looking for alternative methods of storing data, these devices will provide peace of mind to protect your valuable information.
BYOD: Encrypted USB Flash Drives
Encrypted USB flash drives are an essential tool for securely transferring data. These portable devices offer a convenient and efficient way to transport information.
These USBs also ensure your data remains encrypted and inaccessible to unauthorized users. Moreover, it has robust encryption algorithms and password protection.
Lastly, encrypted USB flash drives provide extra security for your data, making them an ideal solution for a BYOD.
One notable example is the Kingston DataTraveler 2000. This encrypted USB flash drive utilizes AES 256-bit hardware encryption. It also features an alphanumeric keypad that requires a user-defined PIN for access.
It is built with a tamper-evident casing, which protects against physical tampering attempts. Its robust device security features make it a reliable choice for those seeking a way to incorporate BYOD methods to protect data.
Another excellent option is the Apricorn Aegis Secure Key 3NX. This encrypted USB flash drive incorporates FIPS 140-2 Level 3 validation. This feature ensures government-grade device security. It also offers a built-in hardware-based PIN pad for secure authentication. It supports hardware-based encryption and decryption, providing high-performance data protection.
BYOD: External Hard Drives With Hardware Encryption
External hard drives with built-in hardware encryption are reliable for larger data volumes. These devices offer spacious storage capacities by employing encryption mechanisms to protect data stored on the drive.
They provide a portable and secure means of transporting data while maintaining confidentiality. External hard drives are also excellent for BYOD settings and to back up important files.
One example of an external hard drive with hardware encryption is the Western Digital My Passport. This series offers models with built-in hardware encryption and password protection.
The Western Digital My Passport also provides ample space to securely store and transport large amounts of data. The rugged design of the Western Digital My Passport ensures durability. Thus, it is suitable for various environments.
BYOD: Secure Portable SSDs
Solid-state drives (SSDs) have gained popularity for their speed and durability. Secure portable SSDs combine these benefits with enhanced security features. This makes them ideal for physically transporting sensitive data.
They offer fast data transfer rates and robust encryption, ensuring data remains protected throughout transportation. It makes a great choice to a bring your own device setup.
An exemplary secure portable SSD is the Samsung T7 Touch SSD. This device combines high-speed USB 3.2 Gen 2 connectivity with fingerprint authentication. The fingerprint sensor provides an additional layer of device security by allowing access only to authorized individuals.
With AES 256-bit hardware encryption and a durable design, the Samsung T7 Touch SSD offers an optimal balance between performance and data security.
BYOD: Hardware-Encrypted NAS Devices
Network-attached storage (NAS) devices with hardware encryption are an excellent local storage option for securely transporting data within a network or across different locations.
These devices provide centralized storage and allow multiple users to access and share files securely. They offer advanced encryption options, ensuring the confidentiality of data during transportation.
The Synology DiskStation DS920+ is a notable hardware-encrypted NAS device. It supports AES-NI hardware encryption acceleration and provides robust security features to protect sensitive data.

The Synology DiskStation DS920+ offers comprehensive data security and collaboration solutions with user authentication, deduplication, and remote access capabilities. It also provides features like snapshot replication, which allows you to create point-in-time copies of data for added data protection and disaster recovery.
Another example of a hardware-encrypted NAS device is the QNAP TS-453D. This device offers AES 256-bit encryption for shared folders, ensuring the privacy and integrity of your data. It also supports advanced device security features such as two-step verification, IP blocking, and anti-malware protection.
With its powerful performance and secure data transportation capabilities, the QNAP TS-453D is an excellent choice for business security and individuals looking to protect their data during physical transportation, such as BYOD, to work.
BYOD: Write-Once Read-Many (WORM) Drives
Write-once-read-many (WORM) drives are designed to prevent data alteration or deletion, making them a preferred choice for industries with strict compliance requirements, such as healthcare and finance.
These drives ensure data integrity by allowing information to be written once and read many times. While not mainly for BYOD, WORM drives offer a secure method of transporting sensitive records and archives.
Sony Optical Disc Archive is a prominent example of a WORM drive solution. It provides ample storage capacities and long-term data retention while maintaining the immutability of stored data.
The system utilizes optical media with specialized write-once characteristics, preventing unauthorized modifications. With its robust archival capabilities, the Sony Optical Disc Archive is widely used in industries that require secure data transportation and long-term data storage.
BYOD: IronKey Secure USB Drives
IronKey Secure USB drives are renowned for their robust security features and military-grade encryption.
These drives are designed to withstand physical attacks and protect against malware threats. They offer a high level of security for transporting data. Thus it is considered one of the best options for bring your own device scenarios.
IronKey D300 is a well-known example of a secure USB drive. It features hardware-based AES 256-bit encryption, encrypting your data at rest and in transit. The rugged design of the drive is waterproof and tamper-resistant, providing durability and protection against physical damage.
IronKey secure USB drives also offer advanced features like self-destruct mechanisms, which erase the data stored on the drive in case of unauthorized access attempts.
BYOD: Encrypted SD Cards
SD cards are commonly used in cameras, smartphones, and other portable devices. Encrypted SD cards are an excellent option to ensure data security stored on SD cards during transportation.
These cards encrypt the data and require authentication for access. It also protects sensitive information from unauthorized users, making it extremely handy in a BYOD setting.
SanDisk Extreme PRO SDXC UHS-II is an example of an encrypted SD card. It offers fast read and write speeds, making it suitable for capturing high-resolution photos and videos. The card utilizes built-in hardware encryption to protect the stored data, ensuring its confidentiality during transportation.
With capacities ranging from 64GB to several terabytes, encrypted SD cards provide a secure and convenient solution for transporting data captured on various devices.

BYOD: Secure External SSDs With Biometric Authentication
For those prioritizing security and convenience, secure external SSDs with biometric authentication provide an excellent solution. These devices combine hardware encryption with fingerprint recognition technology, ensuring only authorized individuals can access the stored data.
Biometric authentication adds an extra layer of security by eliminating the need for passwords or PINs, which can be vulnerable to brute-force attacks. This is a good option when you bring your own device setup.
The iStorage diskAshur BT2 is a prime example of a secure external SSD with biometric authentication. It utilizes AES 256-bit hardware encryption and features a built-in fingerprint sensor for secure authentication.
The device is platform-agnostic and compatible with various operating systems, providing flexibility for users. With its robust security features and user-friendly interface, the iStorage diskAshur BT2 offers a secure and convenient solution for transporting sensitive data.
BYOD: Secure Cloud Storage Devices
While this article focuses on physically transporting data, it is also important to mention secure cloud storage devices. Cloud storage plays a significant role in securely transmitting data over the internet. It has tons of benefits for normal people as well.
Internxt provides military-grade encryption. It assures that your data is encrypted on your device before it is uploaded to the cloud. It remains encrypted while in transit and at rest. This ensures that only you have the decryption keys, enhancing the confidentiality of your data.
With client-side encryption, zero-knowledge architecture, and open source software, Internxt ensures your data is secure and private, even from the service provider.
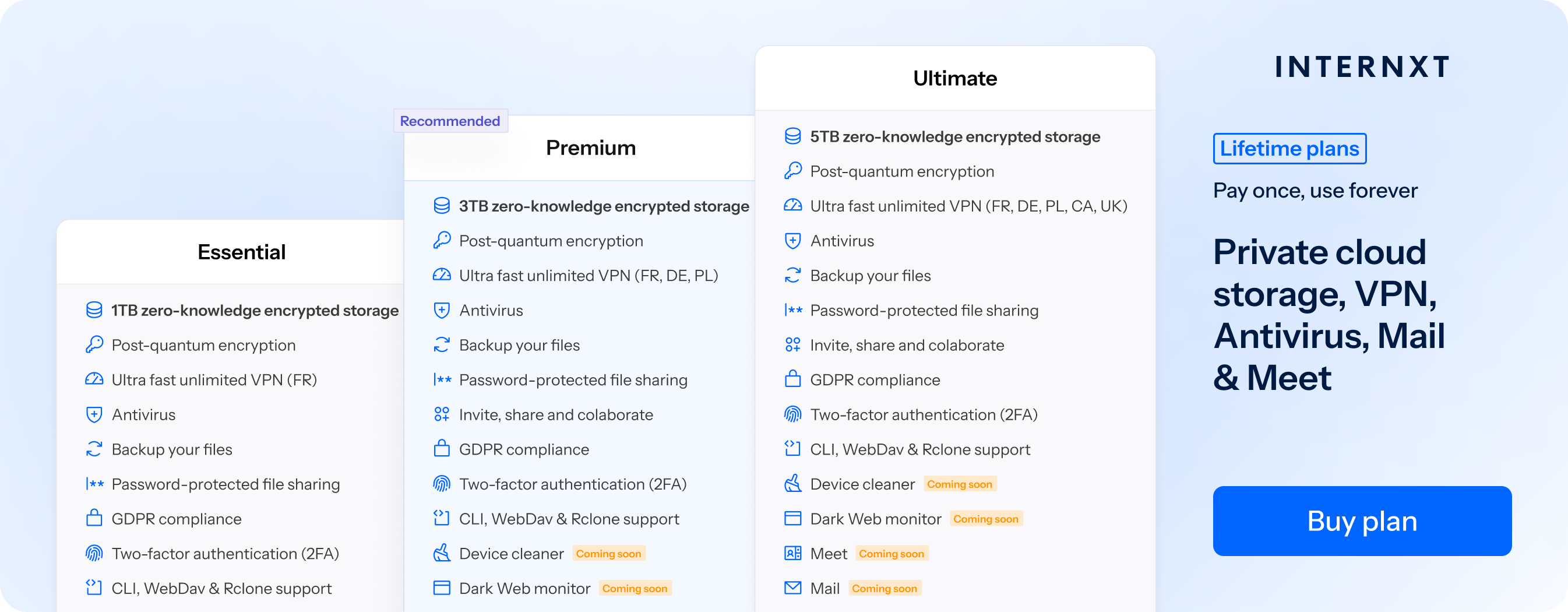
Internxt also allows you to access your files anytime, anywhere. This makes your data solidly secured even if you physically change your locations. Furthermore, you can control who to share your data with. It even has a feature to set how often you want your files downloaded.
BYOD: Secure Portable Hard Drive Enclosures
In some cases, you may already have an internal hard drive that you want to transport securely. A secure portable hard drive enclosure can be a practical solution in such situations. These enclosures provide a protective casing for your existing hard drive while incorporating advanced security features to protect data.
The Oyen Digital U32 Shadow Dura USB-C enclosure is an excellent example of a secure portable hard drive enclosure. It features a rugged aluminum housing with built-in hardware encryption, protecting the data stored on your internal hard drive. The enclosure supports high-speed USB-C connectivity and is compatible with various operating systems, making it versatile and easy to use.
Secure portable hard drive enclosures provide a cost-effective way to repurpose your existing internal hard drives for secure data transportation. By encrypting the data and providing physical protection, these enclosures offer a secure addition to any bring your own device setup.
BYOD: Secure Data Storage Lockers
In situations where physical security is a primary concern, secure data storage lockers provide a robust solution for transporting data physically. These lockers are designed to protect your storage devices from theft, tampering, and unauthorized access, ensuring the integrity and confidentiality of your data.
The DatAshur Personal2 Secure USB 3.2 Flash Drive Locker is a prime example of a secure data storage locker. It combines an encrypted USB flash drive with a rugged aluminum enclosure equipped with a physical lock.
The locker protects against physical attacks and unauthorized access attempts. With PIN-based authentication and military-grade encryption, the DatAshur Personal2 Secure USB Flash Drive Locker offers a secure storage solution for transporting data in high-risk environments.
Secure data storage lockers are especially valuable when transporting sensitive data when physical security is paramount. Such scenarios include during travel, bringing your own device setup, or in high-security environments. They protect your storage devices, ensuring your data remains secure even in theft or loss.
BYOD: Secure Data Transport Cases
Secure data transport cases offer a comprehensive solution for companies looking to implement a strong security policy for an individual who frequently transports multiple storage devices or sensitive equipment.
These cases provide physical protection and advanced security features to safeguard your data during transportation.
The SKB iSeries Waterproof Case with Custom Foam Insert is a secure data transport case example. Its durable and waterproof exterior protects your storage devices from physical damage. The case includes custom foam inserts that securely hold your devices in place during transit. Additionally, you can opt for an integrated combination lock or padlock holes for added security.
Secure data transport cases are particularly beneficial for professionals in photography, videography, and IT, where transporting multiple storage devices is common.
By providing a secure and organized environment for your devices, these cases ensure that your data remains protected from physical damage, theft, and unauthorized access.

BYOD: Safeguard Your Data with the Best Secure Devices for Physical Data Transport
The 12 best-secured devices for transporting data physically discussed in this article provide various options to meet your BYOD needs. Whether you are a business professional, a student, or an individual with sensitive data, these devices offer robust encryption, advanced security features, and user-friendly interfaces.
Data security is a continuous process, and it is essential to stay informed about the latest security practices and updates in device security. Always remember that adopting secure devices and implementing proper security measures can minimize the risk of data breaches and protect your valuable information effectively.
If you want to learn more about cybersecurity, you can enroll in a computer science degree or other relevant courses to learn more about this fascinating topic.

